Is Your Healthcare Data Safe When Outsourcing? 7 Things to Check

Today, businesses can maintain their core operations remotely with technology. While we are indeed in the digital era, this convenience comes with risks, including security breaches. In the healthcare industry, data security is not only essential but also legally required.
Between 2009 and 2020, about 3,705 healthcare information breaches of 500 or more records were reported to the U.S. Department of Health and Human Services (HHS) for Civil Rights. Those security breaches led to the loss, theft, exposure, or disclosure of over 265 million healthcare records.
This terrifying scenario could have been prevented had there been more stringent security measures and protocols in place. In the U.S., Health Insurance Portability and Accountability Act (HIPAA) regulations uplift the patient’s right to protect their health information. Anyone is prohibited from disclosing patient data without the patient’s consent.
7 Things to Check to Ensure Your Healthcare Data is Safe
Below, we break down the things you need to check to ensure the security of your clients’ healthcare data, especially if you depend on healthcare outsourcing, and avoid the worst-case scenarios.
1. Make Sure Your Outsourcing Partner Implements the Principle of Least Privilege
The idea behind the principle of least privilege (PoLP) is that any user, program, or process should only require the bare minimum privileges or permissions to perform certain functions. This computer security concept ensures that with limited access, the “attack surface” is minimized, reducing the risk of internal or external threats.
In healthcare, this can apply in database management. If an employee works to enter patient information into a system, he/she only needs the ability to add to the database. If a malware attack infects that employee’s computer, the attack will be limited to making data entries, and a system-wide infection will be avoided.
2. Certifications and Standards Compliance
It’s vital that your healthcare business only outsources competent and highly-skilled healthcare professionals like medical coders and billers. What’s more imperative is that every professional or outsourcing provider you work with carries certifications that prove their reliability and credibility in handling sensitive data like patient records.
Some of the certifications and organizations that you’d want to keep watch of are the following:
- The American Academy of Professional Coders (AAPC): AAPC’s certifications for healthcare coders are acknowledged globally and regarded as the gold standard in the industry.
- The Healthcare Information and Management Systems Society (HIMSS): HIMSS is a global advisor and thought leader that supports and provides expertise in health information and technology.
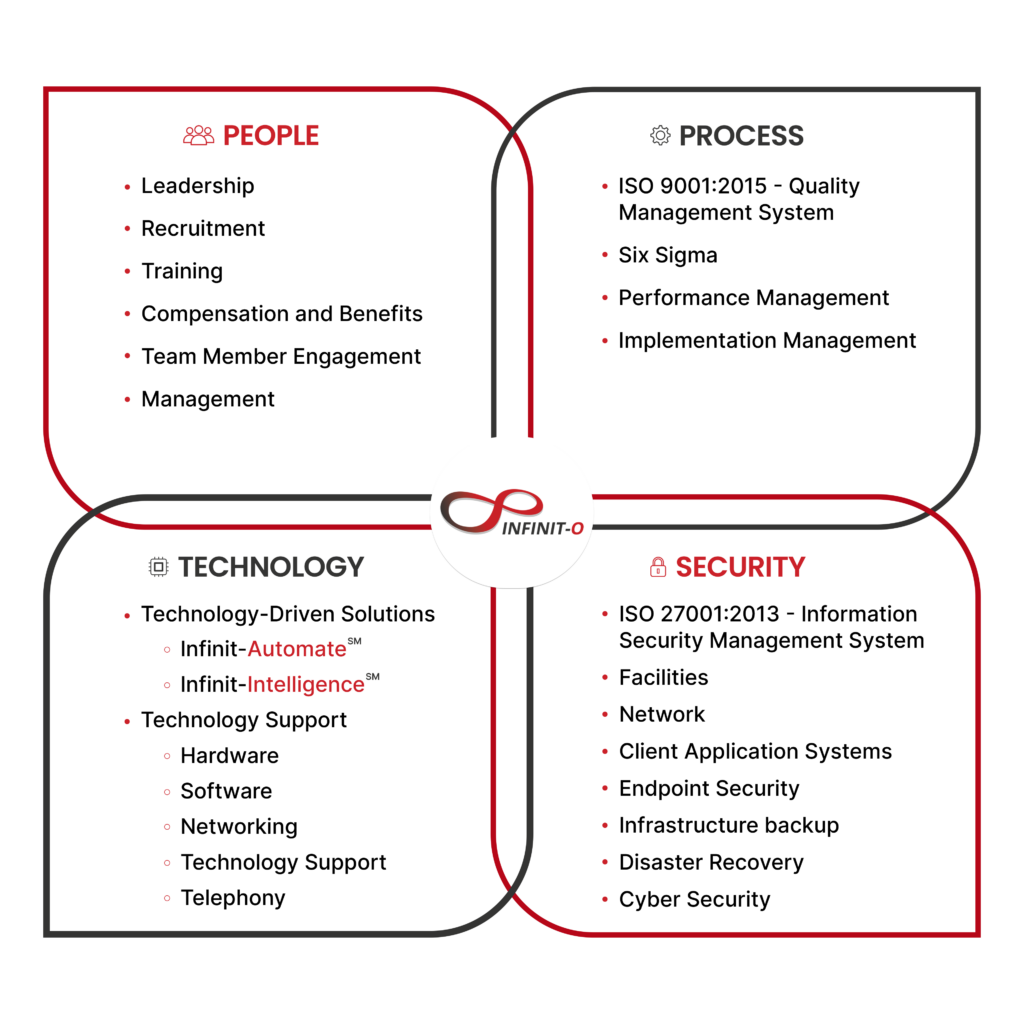
- ISO Certifications on Quality Management Systems and Information Security Management Systems: ISO is well-known for providing requirements for information security management systems to organizations that manage the security of assets.
It’s also worth noting the Net Promoter Score (NPS) of the outsourcing provider, which signifies the loyalty between the company and its customers. A score of 60 and above is a good range that indicates the customer’s satisfaction with a company.
3. Physical Security
Focus on security shouldn’t only be limited to software and cloud security measures. Your IT security or outsource team must also have physical safeguards in place, which can include but are not limited to:
- Implementation of a formal security personnel staff and installation of video surveillance on specific areas
- Workforce training and security management program dedicated to making sure the team is knowledgeable in security threats and risks and HIPAA rules and regulations
- Implementation of facility access restrictions and installing workstation/device security and best practices
- Regular check-up and audit of technical safeguards like hardware, software, data-transmission, integrity controls, and procedural security
4. Intellectual Property Policies
Your company’s intellectual property (IP), whether it’s trade secrets or patient data, is equally, if not more valuable, than your physical assets. You must check with your vendor to make sure they comply with IP laws.
Discuss your privacy and intellectual property policies with your vendor, and ensure that you are aligned with the privacy and intellectual property processes to avoid misunderstandings that can cost you your business resources later on.

5. Employee Training
The safety and security of your company’s data rely on your employees—how they manage and protect them. That’s why it’s crucial that you provide training and education for the people who will handle your sensitive data.
Ask your vendor if they provide training for their medical coders or billers. If they don’t, perhaps it’s better to look for a vendor experienced in the field and known for their proper onboarding, training, and management of employees when it comes to managing company data security.
6. Your Outsourcing Partner Should Conduct Regular Audits for Database Security
Perform regular application, network, and database system security audits. Think of auditing as a preventive measure for your business—it can help determine issues and potential vulnerabilities in your applications, databases, and devices connected to the network.
Conducting audits can also signal any unauthorized access in the network and encourage you to review the adequacy and efficacy of the procedures you have to protect data and handle information risk.
Read more: 6 Tips to Fully Secure Your Healthcare Business
7. Equip Employees with Necessary Tools
While allowing employees to use their personal computer or laptop may reduce costs and is convenient for those under design roles, it may not be best practice for roles dealing with sensitive user and business information, such as in the healthcare industry.
Ensure that your outsourcing partner provides the medical coders with the necessary tools and equipment to perform their tasks. The data should be stored either in a hard disk or a cloud drive encrypted with security and password-protected, so only employees can access the system.
Final Thoughts
Imagine the cost, consequences, and the tarnish to your reputation that dating falls into the wrong hands could bring. With a credible and certified outsourcing partner that employs proper security protocols, not only can you be confident when it comes to security concerns but also save a significant sum on operational cost.
Keep in mind that an outsource service provider with an NPS of >60 will bring you a better sense of security and peace of mind. A high Net Promoter Score means that a company has a proven track record in providing exceptional service. If you want to ensure the security of your healthcare data, you want nothing less than the best.
Work with highly reputable data security outsourcing providers like Infinit-O. We are ISO 27001 and 9001 certified and GDPR-, HIPAA-, and DPA20212-compliant to ensure the confidentiality of your data. Infinit-O’s healthcare outsourcing services will assign a high-performing healthcare team trained to keep your healthcare data safe and adapt to your ever-evolving needs.
Let’s work together to ensure your healthcare data is safe and secure.
Start small. Exceed expectations. Think infinitely. Think Infinit-O.






This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.